How to Add an E-Mail Target
Note: E-mail sources are frequently overlooked sources of sensitive data. ArchTIS Spirion recommends you scan emails and email attachments on a consistent basis to reduce the risk of your sensitive data being exposed and improve your overall data security posture.
Available e-mail targets include:
- Gmail
- Exchange
- Exchange Online
How to Add an Email Target
Use the following steps to add an e-mail Target in Spirion Sensitive Data Platform:
- From the left side navigation menu select Data Asset Inventory > Data Assets and Targets.
- Select the TARGETS tab from the top of the page.
- In the upper right corner of the page, click the blue +Add Target button.
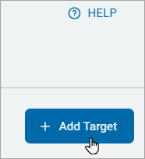
- The Add New Target pop-up window appears.
- Target Name: Enter the name of the Target in the "Target Name" field.
- Under "Target Type," select the Email tile.
- Next, select one of the following e-mail service providers to proceed:
- Gmail
- Exchange
- Exchange Online
How to Add a Gmail Target
To add a Gmail Target use the following steps, as a continuation from the steps above in "How to add an email Target":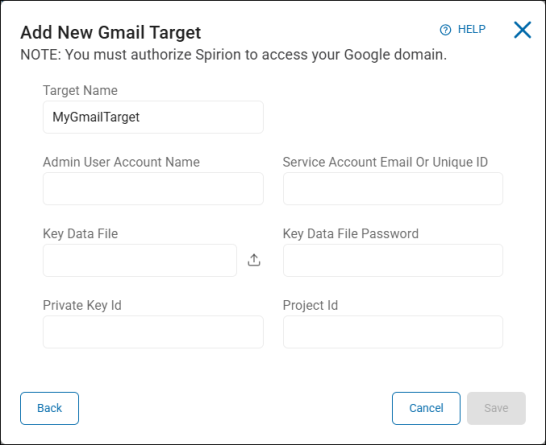
- In the pop-up window "Select an Email Service Provider to Configure," select the Gmail tile under "Email Service Provider Options."
- The "Add New Gmail Target" pop-up window opens. Enter the following information:
- Admin User Account Name: Type the admin user account name.
- Service Account Email or Unique ID: Type the service account email address or unique ID.
- Key Data File: Click the upload icon () to locate a file on your local computer.
- Key Data File Password: Type the password associated with the key data file.
- Private Key Id: Type the private key identification number.
- Project Id: Type the project ID.
- Click the Save button to save, Cancel button to discard, or Back button to return to the previous screen.
How to Add an Exchange Target
Note: For Exchange On-Premise Targets, when content or a file is added in draft form (such as a social security number in a new email in draft status), the location is not skipped on subsequent scans after being scanned the first time. Drafts are excluded from the Search History. This is a known issue.
To add an Exchange Target use the following steps as a continuation from the steps above in "How to add an email Target":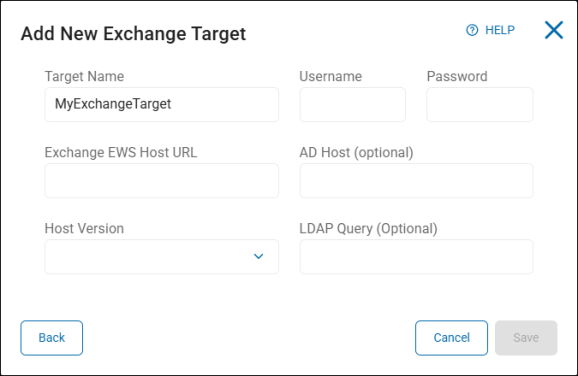
- In the pop-up window "Select an Email Service Provider to Configure," select the Exchange tile under "Email Service Provider Options."
- The "Add New Exchange Target" pop-up window opens. Enter the following information:
- Username: Type the username for the account.
- Password: Type the password associated with the username.
- Exchange EWS Host URL: Type the full URL of the Exchange EWS host.
- AD Host (optional): Type the host name. This is optional.
- Host Version: Click an option from the drop-down list.
- LDAP Query (Optional): Type the query. This is optional.
- Click the Save button to save, the Cancel button to discard, or the Back button to return to the previous screen.
How to Add an Exchange Online Target
When you add an Exchange Online Target, you configure one of the following methods of authentication:
- Spirion Hosted Authentication
- Self Hosted Authentication
- Create an Azure App (Optional)
Note: For Exchange Online Targets, Spirion added the ability to authenticate using an (user configured) Azure app. Note this requires Spirion Agents version 13.5 or later. If you attempt to use this method with Agents earlier than v13.5, an EPS failure occurs requiring the reboot of the machine or manual intervention.
When creating a new scan, you are notified of the agent v13.5 requirement if you are attempting to scan an Exchange Online Target: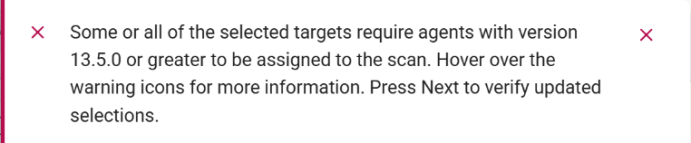
If you assign Spirion Agents to a scan that are version pre-13.5, you receive the following message which prevents the scan from being run: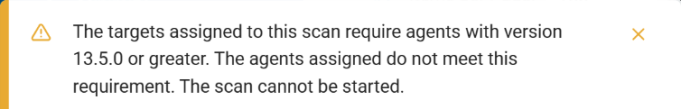
To add an Exchange Online Target use the following steps as a continuation from the steps above in "How to add an email Target":
Procedure:
- In the pop-up window "Select an Email Service Provider to Configure," select the Exchange Online tile under "Email Service Provider Options."
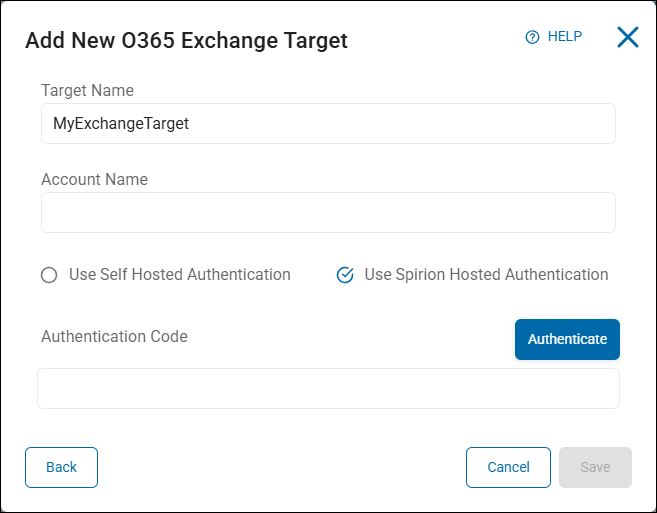
- The "Add New O365 Exchange Target" pop-up window opens. Enter the following information:
- Target Name: Type the Target name.
- Account Name: Enter the admin account user name
- Spirion Hosted Authentication:
- Select (check) the Use Spirion Hosted Authentication radio button.
- Click the blue Authenticate button.
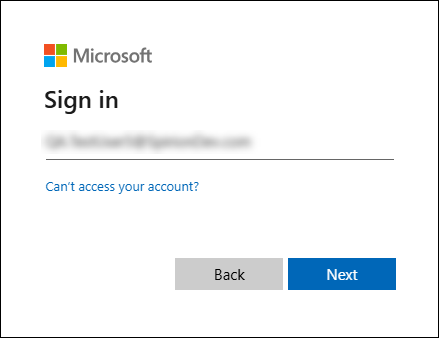
- This takes you to the Microsoft (Office 365) login page where you enter the same Admin user account from the previous step and complete the login process.
- You are asked to authorize claims to create the “Spirion Azure App”.
- Accept the claims. The Spirion Azure App is created. The browser page is redirected to a loopback page with the URL “127.0.0.1/code=xxxx”.
- Select and copy the entire URL.
- Paste the URL into the Authentication Code box.
- Click the Save button to save the Target or the Cancel button to discard.
- Self Hosted Authentication:
- Target Name: Enter the Target name.
- Account Name: Enter the admin user account name
- Select Use Self Hosted Authentication
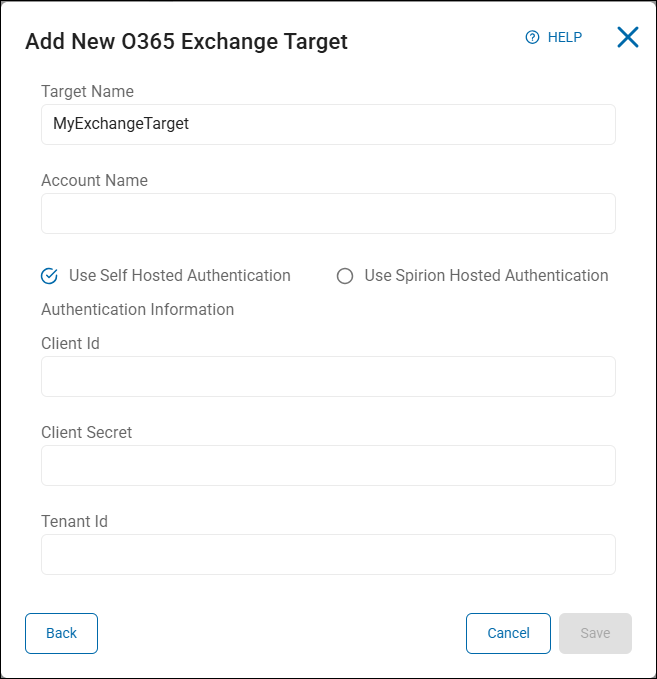
- Enter the following information from your Azure App. If you do not have an Azure App, see "How to Create an Azure App (Optional)" below:
- Client ID – Enter your Client ID
- Client Secret – Enter your Client Secret
- Tenant ID – Enter your Tenant ID
- To confirm your Azure App has the necessary permissions, see "How to Add API Permissions to Your Azure App," below.
- Click the Save button to create the Target, the Cancel button to discard, or the Back button to return to the previous screen.
- This completes the authentication process.
How to Create an Azure App (Optional)
If you do not have an Azure App, use the following instructions to create the app and record the information you need to create your Exchange Online Target.
How to Create a New App Registration
Use the following steps to create a new App registration:
- Log in to the Azure Portal
- Search for and select Microsoft Entra ID. See the image below.
- Select App Registrations under Manage on the left side menu. (Alternatively, click "Add application registration" under Quick Actions at the bottom of the page)
- Click New registration
- Select one of the first two radio buttons based on your needs:
Note: Redirect URI is not required - Accounts in this organizational directory only (YourDev only - Single tenant)
- Accounts in any organizational directory (Any Microsoft Entra ID tenant - Multitenant)
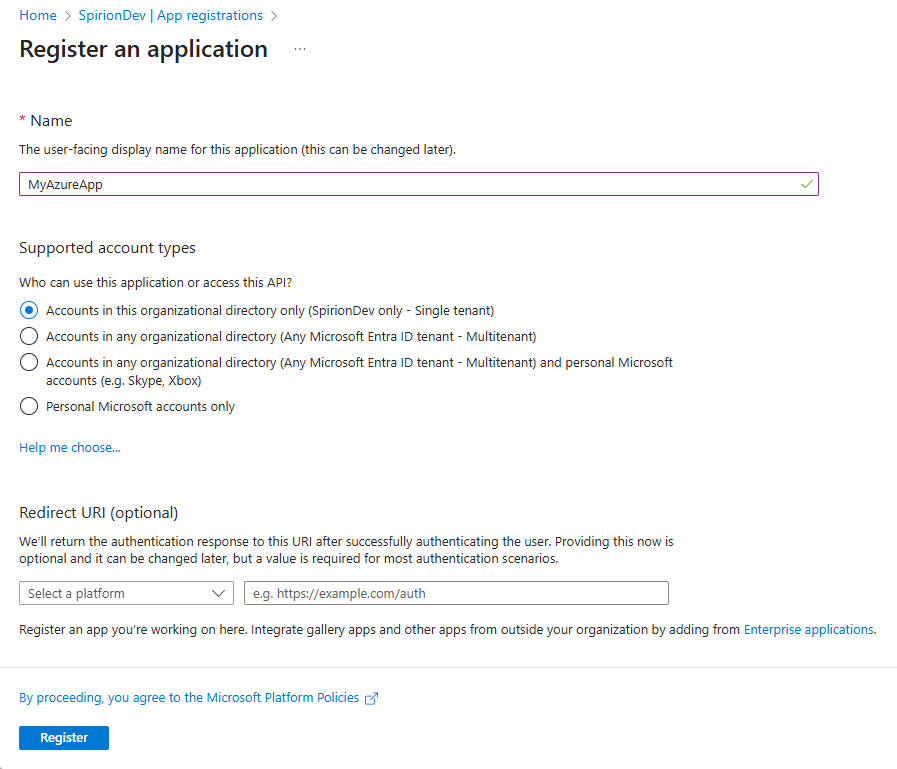
- Click the Register button at the bottom of the page.
Note the IDs
Record the following information:
- Application (client) ID
- Directory (tenant) ID
How to Configure Certificates and Secrets
Use the following steps to configure certificates and secrets:
- From the left side menu, under "Manage," click Certificates & secrets
- Click +New client secret.
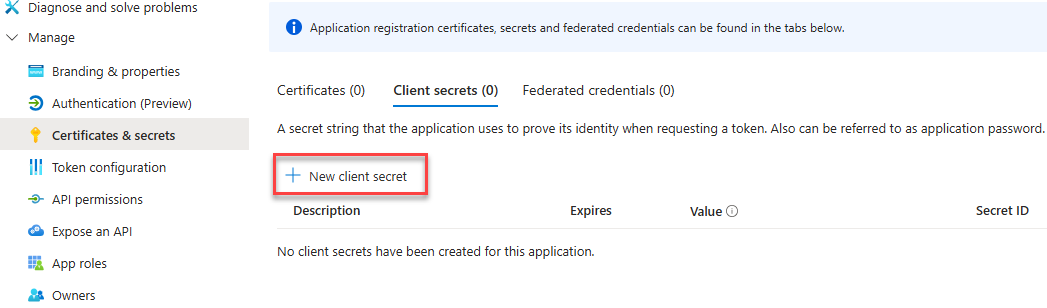
- Enter an appropriate name and record the name.
- Record your Client Secret Value and Secret ID.
NOTE: You will not have access to your client secret again.
How to Add API Permissions to Your Azure App
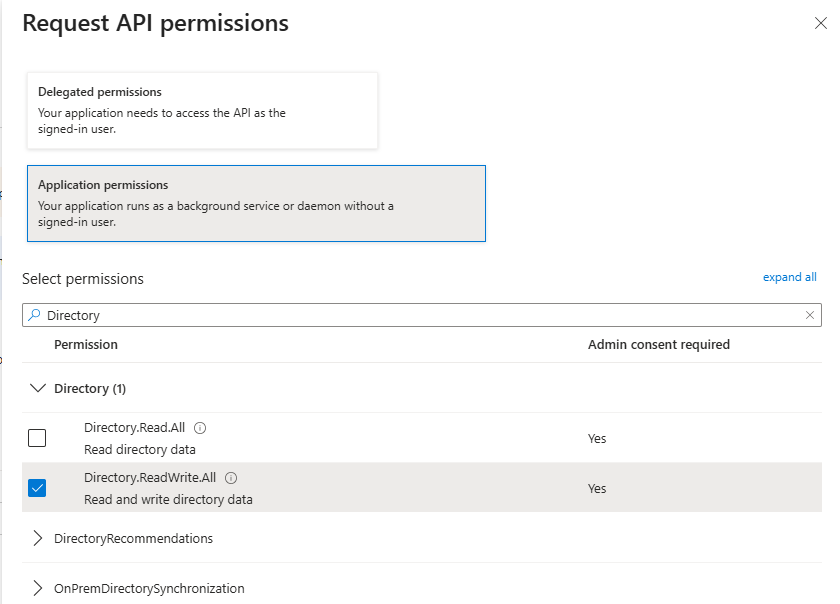
Use the following procedure to add the required API permissions to your Azure App (see "Required Azure App API Permissions" below):
- One the left side menu, under Manage, select API Permissions
- Click Add a permission
- Select Microsoft Graph at the top of the collection of APIs.
- Select Application Permissions
- In the Select permissions search field type the name of each permission to find it in the list and then select it. See below.
- Click the Add permissions button at the bottom of the pane.
- Repeat this process for each required permission.
- Grant Admin consent to the permission, if necessary.
How to Add the Required Azure App API Permissions
Ensure the following Microsoft Graph permissions are enabled for your new Azure app:
- Files.ReadWrite.All
- Type: Application
- Admin consent required: Yes
- Description: Enables the app to read, create, update, and delete all files the service account user can access.
- Mail.ReadWrite
- Type: Application
- Admin consent required: Yes
- Description: Grants the app access to all mailboxes in an organization and enables the app to access mailboxes without a signed-in user.
- User.Read
- Type: Delegated
- Admin consent required: No
- Description: Enables the app to read basic company information of users.
- User.ReadWrite.All
- Type: Application
- Admin consent required: Yes
- Description: Enables the app to read and write all properties of user profiles.



