What is Residual Data and Why is it Important?
What is Residual Data?
Residual data, also known as ambient data, refers to information that remains on storage devices even after attempts to delete or erase it.
- This occurs because when your data is deleted, the operating system often only removes the pointer to the data, making the space available for new information, but not necessarily erasing the data itself.
- The data physically remains until it is overwritten by new data.
Why Residual Data Matters
Residual data poses a significant security risk for individuals and organizations because it can be recovered using specialized tools and software, potentially exposing sensitive or confidential information.
Studies have shown that a significant percentage of used devices like hard drives, cell phones, and memory cards still contain recoverable residual data, putting the original owners at risk of data breaches and privacy threats.
Key concerns include:
- Data Leakage and Unauthorized Access: Residual data can lead to data breaches if recovered by unauthorized individuals or entities.
- Privacy Violations: Sensitive personal data, such as financial details, photos, and log-in credentials, can be recovered from devices and used for malicious purposes.
- Compliance Issues: Regulations like GDPR require organizations to properly handle and erase personal data, and failing to address residual data can lead to non-compliance.
- Impact on Digital Forensics and Cybersecurity: Residual data is a crucial factor in digital forensic investigations and risk assessments, as it can reveal information about past activities and vulnerabilities.
Residual Data in Spirion Sensitive Data Platform
- The Sensitive Private Information Dashboard (SPIglass™) in Residual Data in Spirion Sensitive Data Platform uses a graph named Inherent Risk to display the risk of the data in your environment at any given point in time.
- Inherent Risk displays Compensating Controls data and Residual data over time as well as the affected locations.
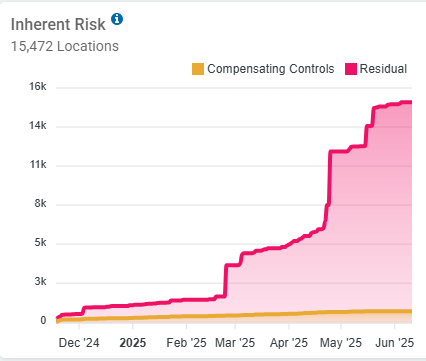
- Inherent Risk displays Compensating Controls data and Residual data over time as well as the affected locations.
Real-World Example: Sensitive Data Can Hide Anywhere & Everywhere
Within a corporate network is an individual machine with an Exchange email account. That account contains an deleted email which contains an attachment - a PowerPoint presentation. That PowerPoint file contains a slide with an inserted bar graph made by Excel.
All the underlying Excel data was embedded, including thousands of Social Security numbers. The SSN are recoverable by a hacker with specialized software. This data is NOT secure and is considered exposed data.
